Yesterday I read an article about a series of art pieces created by Andy Bauch with $10,000 of cryptocurrency hidden in them. Each of the pieces is assembled out of lego bricks.
(Don't read this if you don't want spoilers).
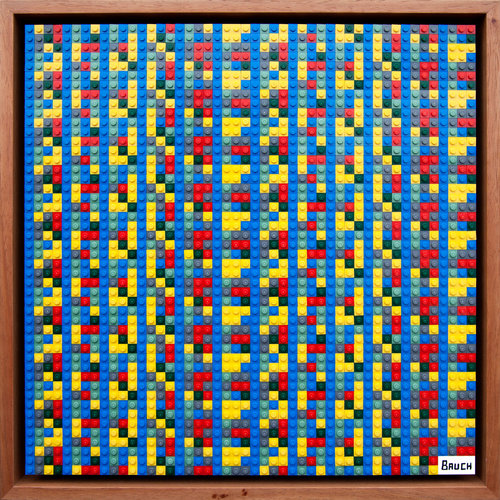
"Bitcoin Initially Valued at $60", by Andy Bauch
Each of the images is named after the value of the Bitcoin it was initially funded with, but each one is now worth substantially more due to the increase in the Bitcoin price.
You can look at the rest of his art on his website.
Today I claimed the BTC from 3 of the pieces, totalling ~0.35 BTC (~£2200). SopaXorzTaker announced on Twitter that he claimed the BTC from another two, and the other pieces in the same series have also been claimed, although it's not clear who did it.
After I told Emma that I was working on this, she read up more about the artwork, and eventually found Andy's New Money Crypto Prices page which lists the names of the art pieces along with the amount of BTC in the addresses. It also reveals what the addresses are, which allowed me to find out which pieces remained unsolved, and therefore which ones to focus my efforts on. This was a big help as time was of the essence, with other people clearly carrying out the same steps at the same time.
I ended up sweeping the ones that were initially valued at $40, $50, and $60.
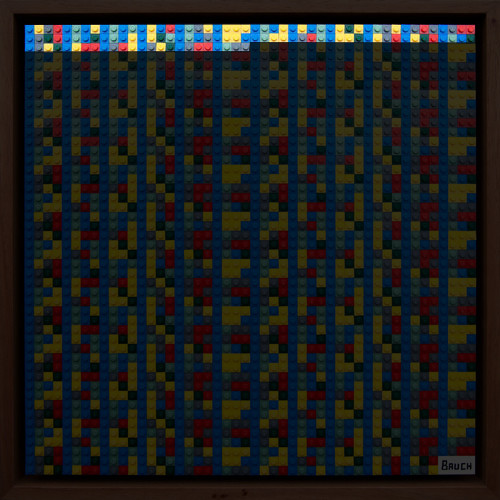
Andy's encoding scheme is quite cool. He created private keys by taking the SHA256 of a 30-character base58 string (a minikey, although I only found this out later - I had assumed he was just using SHA256 of random alphanumeric strings used like brainwallets). He then encoded the ASCII byte values of the characters in the minikey as numbers in various bases (the "initial value $20" painting was base 2, $30 was base 3, $40 base 4, etc.). He then encoded those base-N numbers by using one Lego brick per digit, and one colour for each possible value. The artwork is then just this encoded private key repeated over and over again.
(I've highlighted one instance of the private key in the $60 image here. The rest of the bricks are just repeating the same pattern.)
I manually transcribed the colours of the bricks into a series of letters, double-checking to make sure I got each one right. This was quite laborious! The $60 image became:
BYGRBLBYBLBLBYBRBLGYBYYYBLBYBYBLBYFYBLGYBGRGBGRR
BGFRBLBFBLBYBYFLBLBGBYYBBLYYBGRLBYYFBYGRBYFRBLBF
BGYFBYRRBGRYBGYFBGRRBLGGWhere B is blue, Y is yellow, G is grey, R is red, F is green, L is light blue.
There are several possible ways Andy could have mapped the numbers to a Bitcoin key. It could be the raw byte values of the key, it could be a hex representation of the byte values of the key, it could be the password for a brainwallet/minikey, or any number of other schemes. Given the pattern of blue bricks at every 4th position, I surmised that the number was not selected at random from a uniform distribution of all possible values, which implied most likely the data being represented was ASCII. This assumption turned out to be correct.
I wrote a very dirty Perl script to iterate over every possible mapping of the letters to digits in base 6, and then use the numbers as byte values, and output the subset of corresponding strings that contain entirely printable ASCII. Here are the possibilities for the $60 image.
4mo(y+m'CybdjqmEn*sc/4FqS@aSdz
5mo)y+m'=yhkepm?n*si.5ApRGgRkz
RnoLtVnKht=@FqnimTz?YRjq5d>5@s
SnoMtVnKbtCGApncmTzEXSep4kD4GsI used bitaddress.org's brain wallet tool to convert these strings into the corresponding bitcoin keys, and used blockchain.info to check each address to see which ones had ever had any transactions on them. Once I found the one that had some funds (just imagine my excitement!) I used Electrum to sweep the private key into a wallet under my own control, and the money was mine.
You can see the transaction history for the address 1HvEJG5JR84MVpncXcDVBqx65uY5odr6fP on blockchain.info.
In hindsight, I could have cut down my manual search space if I knew he was using minikeys: instead of looking for any printable ASCII characters, I could restrict the character set to only the base58 characters, and additionally the first character must be a capital S.
Having solved the $60 image, I repeated the same steps on the $40 (base 4) and $50 (base 5) images, to great success.
I didn't actually expect to be able to solve any of the artwork, and even if I did solve it I didn't expect to be the first one to do so. It was all a pleasant surprise, and extremely exciting.
In fact the whole thing was so fun that I intend to copy Andy's idea and make a Lego Bitcoin key art piece of my own. (Update 2018-03-25: I've made a little tool to help generate the grids: Bauch-style Lego Artwork Generator).
Here's what we can reconstruct as a timeline of the solving of the puzzles:
| Time | Image | Value | Address | Solved by |
|---|---|---|---|---|
| 2018-03-23 21:04 | $70 | 0.16 BTC, £1000 | 12g5BNdmKvHDQXqk37uGEDWDX9AiH7Siuz | Unknown |
| 2018-03-23 23:03 | $90 | 0.21 BTC, £1300 | 16DLhNnN82xAdLKr6DDCnPBmUZ26qcjFhC | Unknown |
| 2018-03-24 12:21 | $20 | 0.046 BTC, £290 | 1NmxAV1ze28U4Uuqg2fH1JTB8NtWKvTyhM | SopaXorzTaker |
| 2018-03-24 13:20 | $30 | 0.07 BTC, £430 | 17kdWzib9nnQ3KJJ9LkJyN7nxehb9NuufP | SopaXorzTaker |
| 2018-03-24 14:26 | $80 | 0.19 BTC, £1200 | 1PT9sjy7J9H5271a7GWKeu4C5iDpTFuWTW | Unknown |
| 2018-03-24 14:34 | $60 | 0.14 BTC, £870 | 1HvEJG5JR84MVpncXcDVBqx65uY5odr6fP | jes |
| 2018-03-24 14:48 | $40 | 0.09 BTC, £560 | 1EbcjT4DxkHQbp5qe6ALrsNDHfGqXozJdc | jes |
| 2018-03-24 15:47 | $50 | 0.11 BTC, £680 | 1PTsXZrFjFBieS9E4oHT6TcmEXbFDatD9K | jes |
Although I've not checked, I assume the $70 and $90 images use the same kind of encoding scheme as all the others, so it's not obvious to me why the person (or people) who solved those didn't swipe the others during the following 12 hours.